-ND^ZWAAMGNCAC/APSRCYINBU-U>/BAKME
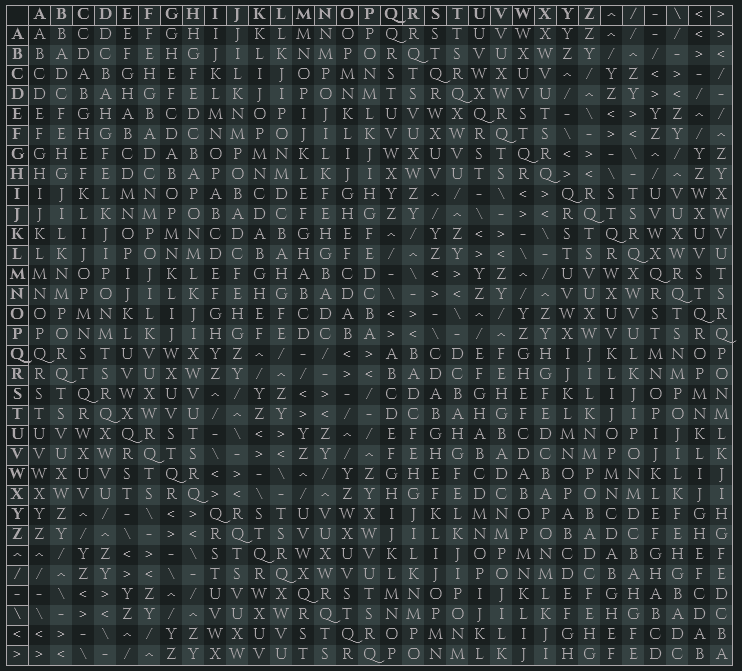
The Ettinnay Cipher is a polyalphabetic substitution cipher that originated in Ettinnay but is now in common use across all of Eynoria. It is widely considered unbreakable without the encryption key. The alphabet is 32 characters long, the last 6 are typically used as dummy characters or as substitutes for punctuation. The cipher is symmetric, the same key is used to both encrypt and decrypt.
Cipher Square
Examples
If we wanted to send somebody the message "Meet me by the river", and we used the key "apples", we would proceed as thus:
First, let's replace the spaces with the character "-" to get our plaintext. Second, our plaintext is 20 characters long, so we repeat our key to get our keytext.
| plaintext |
MEET-ME-BY-THE-RIVER |
| keytext |
APPLESAPPLESAPPLESAP |
We can now encrypt our plaintext using our keytext. We take the first character in the plaintext and the keytext and look them up with the cipher square above. We then repeat this for each character in the plaintext. The first 6 characters gives us the following:
| plaintext |
keytext |
ciphertext |
| M |
A |
M |
| E |
P |
L |
| E |
P |
L |
| T |
L |
Y |
| - |
E |
Y |
| M |
S |
< |
| E |
A |
E |
After encrypting all the characters this way, we end up with our ciphertext: "MLLYY<ETOTYBHLT^MHE<".
Ciphertexts can be decrypted in the exact same way as encrypting, as long as you know the key. Using the same method used to encrypt the last message, try to decrypt the message "XLANKDOUYMVAI<HAYMXNDLV>" with the key "emeralds".
Plaintext answer
History
The Ettinnay Cipher was first devised at some time around 280 Era of Man. The First Ettinnay Coalition was looking for a more robust encryption method for securely sending messages between generals. If the messages were intercepted, they wouldn't able to be decrypted without knowing the encryption key.
After the Spiritmeld in 1 Era of Spirits, Refugees from Ettinnay spread the secrets of the Cipher across the rest of Eynoria. It is now in common usage where secure written communication is required.
The
Order of the Raven makes extensive use of the Ettinnay cipher, with it's vast network of Chapters and agents.
Weaknesses
Widely considered to be an unbreakable cipher, it does in fact have some weaknesses. The length of the key is a major factor, small keys repeat themselves making repeating patterns in the ciphertext vulnerable to attack. Weaknesses may exist within the plaintext itself. For example, starting a letter by addressing the recipient by name could be used to derive the key if the key repeats itself within the span of the address.
A character encoded with "A" always encodes as itself, and a character encoded with itself always encodes as "A".
Other avenues of attack may exist.

This is so impressive. I had to take some time to understand how it works, but wow, amazing. I have put the blocklink to your article in my SC journal, hope that's okay. I am collecting some of my fav SC articles.
Awesome! Thank you!