Using simple text cyphers in your games
Introduction
This article will present motivations, creation, and usage of simple text cyphers for creating written messages, markers, and missives. These methods can be pictorial chalk marks on cavern walls, missives between troops/henchman, spy networks, or even to represent written language. They can be used to provide challenges to the player's directly or in conjunction with their character's skill sets and linguistic knowledge. This article begins with a focus on two methods, substitution and Morse Code, and then concludes with ideas for incorporating encoded messages can be integrated into your game or campaign.Cyphers
Simple substitution cyphers
Perhaps the simplest form of cypher is substitution, where a singular letter is substituted with another. Shifting - Simply, this method shifts the letters/characters of the message by a constant index like 3. If you think of the latin based English alphabet of a-z as a loop, a becomes d, b becomes e, until z becomes c and completes the loop. With 26 characters in this alphabet, the index range is from 2 - 25 and can be negative where with an index of -3 where a becomes x, etc.
Example (index of 5): Move your troops to take the right flankapplying the cypher method results in: rtaj dtzw ywttux yt yfpj ymj wnlmy kqfsp
You can simply reverse the alphabet, where a becomes z, z becomes a, etc.
Example (reversed): Move your troops to take the right flankapplying the cypher method results in: nlev blfi gillkh gl gzpv gsv irtsg uozmp
In the above examples, the word length remains consistent with the original message. To obfuscate further, consider adding a space as its own character in the cypher, resulting in a 27 character circle.
Example (index of 7, space inclusive): Move your troops to take the right flankapplying the cypher method results in: tvblgevayg yvvwzg vg hrlg ogypno mshur
Morse code based cyphers
A different set of substitution cyphers can be created based on Morse code. Morse code is a method that encodes each letter of the alphabet into a series of "." and "-" where letters (and numbers) do not have a uniform length. There are several refinements and extensions to include punctuation, but this article will limit itself to the International (ITU) standard. You can choose your own pairings of substitution glyphs including Cyrillic, Greek, Unicode symbols to create hundreds of different variants, enough to keep your players challenged and a message (if used to represent a language) hidden from the characters until they can locate assistance with the translation/decryption.
Be creative, you can use the Morse Code with any phonics, for example a "." can be "uh" and a "-" can "hu." Make a recording of the message and play it back to represent a conversation being overheard. Example: Move your troops to take the right flankapplying the cypher method results in: -- --- ...- . -.-- --- ..- .-. - .-. --- --- .--. ... - --- - .- -.- . - .... . .-. .. --. .... - ..-. .-.. .- -. -.- Substituting a "/" for "." and a "\" for a "-" Example : Move your troops to take the right flank
applying the cypher method results in: \\ \\\ ///\ / \/\\ \\\ //\ /\/ \ /\/ \\\ \\\ /\\/ /// \ \\\ \ /\ \/\ / \ //// / /\/ // \\/ //// \ //\/ /\// /\ \/ \/\ Substituting a "<" for "." and a ">" for a "-" Example (morse code): Move your troops to take the right flank
>> >>> <<<> < ><>> >>> <<> <>< > <>< >>> >>> <>>< <<< > >>> > <> ><> < > <<<< < <>< << >>< <<<< > <<>< <><< <> >< ><>
Complex (combined) cyphers
The Morse Code method above uses spaces (or in the case of audible representation, a pause) and suffers from singular character delineation. To further mask the original message, you can combine the Morse Code with a substitution ring (see above).Bacon's Cypher (variant)
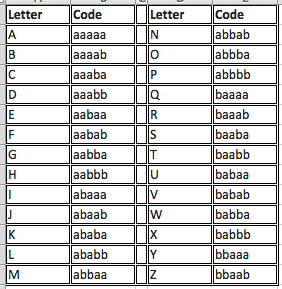
Another plain text cypher is Bacon's cypher which is not vulnerable to the same singular character delineation mentioned previously. Bacon's Cypher uses five characters/glyphs to represent the alphabet. The original Bacon cypher used a single combination to represent both i and j, as well as a single combination for u and v. A variant exists that distinguishes these and is used here. Example: Move your troops to take the right flankapplying the cypher method results in: abbaaabbbabababaabaa bbaaaabbbaubaaab baabbbaaababbbaabbbaabbbbbaaba baabbabbba baabbaaaaaababaaabaa baabbaabbbaabaa baaababaaaaabbaaabbbbaabb aabablaaaaaabbabababa Each of the above methods have vulnerabilities (word and character distinction) but can still help a game master present a variety of messages that the characters have to get creative to decode.




Comments